In the case of content platforms that are just starting out, it's often a combination of excitement and anxiety. Excited because the number of users is growing, anxious because the servers are extremely susceptible to “intermittent outages” whenever there is an overload of traffic. The biggest headache is not the normal range of user concurrency, but the seemingly inexplicable garbage traffic.
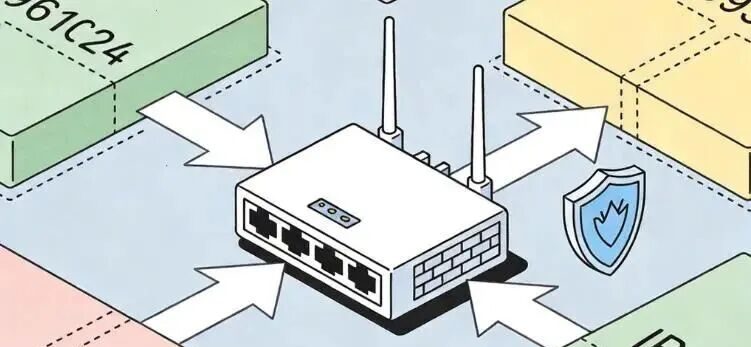
In fact, in many cases, through IP isolation to prevent DDoS attacks this way is the most direct, but also has the most cost-effective means of defense. Many practitioners are accustomed to all the business logic, databases and static resources are stacked under the same public IP. This is in the hacker's point of view, it is equivalent to a completely unarmored warrior, as long as the other side wants to cut off the services provided, directly to the only IP to blast the bandwidth can be achieved.
Designing a technical program is the same thing as running a personal IP, you have to learn to build a moat for yourself first.
The essence of DDoS attack is simply a kind of “traffic bullying” behavior. The other side will use a large number of botnets to launch related requests to the server, until the bandwidth resources completely burst, or the CPU computing power to all exhaustion. At this point, if the core business IP is exposed directly to the front line, it is basically defenseless. Seen a lot of teams, in the attack suffered the first reaction is to go to increase bandwidth, the result of the other side of the attack will be the magnitude of the purchase of bandwidth than dozens of times more, this way of hard to carry often belongs to the most money and lack of effect.
The more common recommended practice is to hide the “real address” of the business.
The first step is to set up a proxy or distribution node at the outermost layer of the business. This layer of nodes is like a security checkpoint through which all access requests must pass. In this way, only the proxy IPs are visible to the outside world, and the real source IPs are hidden in the depths. When an attack occurs, the firepower will be focused on these proxy nodes, while the core database and business logic can still run smoothly in the background. This relies on the physical or logical level of IP isolation to prevent DDoS attacks, the logic behind it is very simple: since it can not prevent the other side of the bombing, then let the other side can not find the door in what place.
In this process, there is a detail that many people ignore, that is, “back to the source of security” this aspect. Even if the proxy has been used, if the source server's firewall does not set up a good whitelist, as long as the attacker through some technical means to scan out the real IP, they can still go to bypass the outer layer of protection to directly attack the core part. Therefore, it is important to set up the bottom of the server: only allow IP access from the proxy node, and all other requests should be intercepted at the door.
This mindset is actually very inspiring. Whether you're working on server security, running content, or building a personal brand, the thing to do is always to save your limited energy for the core.

Many creators, in the process of carrying out the process from 0 to 1, will be bogged down by all kinds of technical difficulties or miscellaneous trivialities, resulting in the inability to go to a consistent output. For example, some people have spent half a month researching how to prevent attacks, but the result is that not even one piece of serious content has been posted. In fact, professional things can be handed over to professional logic to deal with, in this regard is the same in the content output, you can use the DouDouSheep software to support more than 20 kinds of creation of efficient tools, which can help people to significantly reduce the threshold of these cumbersome links, so that people will be the defense of the energy as well as the rhythm of the creation of the separation.
Back to the defense. In addition to hiding IPs, consider implementing “multilevel isolation”.
For example, the core business is split into different modules, and each module uses a different IP segment to carry out isolation work. When one of the modules is targeted, the other modules will not be implicated. This “divide and conquer” strategy can greatly enhance the resilience of the system. To this point, the use of IP isolation to prevent DDoS attacks is no longer just a simple technical action, but evolved into a set of three-dimensional protection network.
Don't go for that absolute, airtight defense, because that kind of thing doesn't exist. True security comes from having enough of a buffer zone when problems occur to allow the core business to keep breathing in the midst of the storm.
If you are now facing the plague of servers going down every now and then, don't rush out to buy those extremely expensive protection packages just yet. Go back and look at the architecture and see if all the core assets are out in the open. Learning to hide your business behind a barrier is not just a technical skill, it's a safeguard for long-termism.
Carrying out projects, operating IP, the fight to the end is actually to see who can be more stable. Close the door, build the wall higher, and leave the rest to time.


